DefenseWall HIPS 2.44
Free Trial Version
Publisher Description
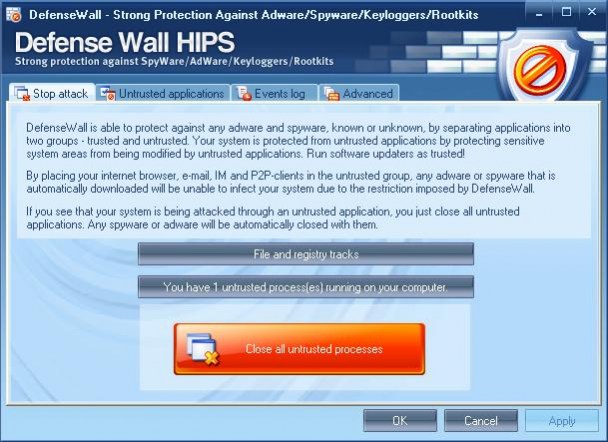
DefenseWall is the easiest way to protect yourself from malicious software (spyware, adware, keyloggers, rootkits, etc.) when you surf the Internet! Using next generation proactive protection technologies, sandboxing and virtualization, DefenseWall helps you achieve a maximum level of protection against malicious software, while not demanding any special knowledge or ongoing online signature updates. No signatures, no popup windows, no false positives. It is just reliable and transparent protection, easy to use and strong.
DefenseWall divides all applications into Trusted and Untrusted groups. Untrusted applications are launched with limited rights of modification of critical system parameters, and only in the virtual zone that is specially allocated for them, thus separating them from trusted applications. In the case of penetration by malicious software via one of the untrusted applications (web browsers, etc), this cannot harm your system and may be closed with just one click! With DefenseWall, Internet surfing has never been so easy and safe. Try it today, and you will be convinced!
About DefenseWall HIPS
DefenseWall HIPS is a free trial software published in the Antivirus Tools list of programs, part of Security & Privacy.
This Antivirus Tools program is available in English. It was last updated on 02 April, 2024. DefenseWall HIPS is compatible with the following operating systems: Windows, Windows-mobile.
The company that develops DefenseWall HIPS is SoftSphere Technologies. The latest version released by its developer is 2.44. This version was rated by 1 users of our site and has an average rating of 5.0.
The download we have available for DefenseWall HIPS has a file size of 3.15 MB. Just click the green Download button above to start the downloading process. The program is listed on our website since 2008-06-27 and was downloaded 74 times. We have already checked if the download link is safe, however for your own protection we recommend that you scan the downloaded software with your antivirus. Your antivirus may detect the DefenseWall HIPS as malware if the download link is broken.
How to install DefenseWall HIPS on your Windows device:
- Click on the Download button on our website. This will start the download from the website of the developer.
- Once the DefenseWall HIPS is downloaded click on it to start the setup process (assuming you are on a desktop computer).
- When the installation is finished you should be able to see and run the program.